How to Integrate LDAP with AEM ? | AEM Community Blog Seeding
How to Integrate LDAP with AEM ? by Aemrules
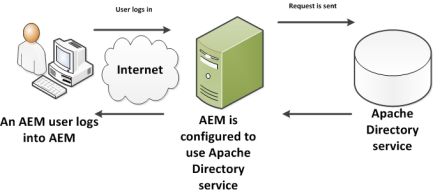
Abstract
LDAP (the Lightweight Directory Access Protocol) is used for accessing centralised directory services. You can achieve below vital things with LDAP integration The User accounts can be synchronised between LDAP server and the AEM repository. The AEM uses LDAP authentication to authenticate users, with credentials being passed to the LDAP server for validation. To improve performance, successfully validated credentials can be cached by repository, with an expire timeout. This helps reduce the effort required to manage user accounts as they can be accessed by the multiple applications. When a user/account is removed from LDAP server validation is no longer granted & access to the AEM is denied. The following are the AEM steps for integrating the LDAP and using it as your Single Sign On (SSO) source of truth for authenticating AEM Users. In order to have LDAP working with AEM, you need to create three OSGi configurations: An LDAP Identity Provider (IDP). A Sync Handler. An External Login Module. 1- LDAP Identity Provider (IDP) The LDAP Identity Provider is used to define how users are retrieved from the LDAP server. Open system console config manager ( /system/console/configMgr) Search for Apache Jackrabbit Oak LDAP Identity Provider Create a new LDAP Identify Provider using plus sign. Use most of the out of the box configuration except for the following values LDAP Provider name - name of the LDAP provider LDAP Server Hostname - Host Name of Provider. LDAP Server Port - Port of LDAP Server. check with LDAP admin if not sure. Bind DN - DN that is used for bind. for example enter value as uid=admin,ou=system Bind Pwd - Corresponding DN password User base DN - Base DN for user searches, Enter value as dc=example,dc=com User id attribute - name of user attribute. Enter value as uid
Read Full Blog
How to Integrate LDAP with AEM ?
Q&A
Please use this thread to ask the related questions.

