AEM Security Best Practices: Awakening to the Need for Better Cybersecurity
AEM Security Best Practices: Awakening to the Need for Better Cybersecurity
Adobe Experience Manager takes security seriously since Adobe, at large, is more than aware just how much is at stake. The average cost of a data breach amounts to $4.24 million according to a 2021 IBM report. AEM security best practices are woven into AEM software so that teams can prevent, quickly detect, and eliminate even the slightest deviations.
In this article, you’ll learn what contributes to the overall Adobe AEM security, determine what cyber threats any CMS such as AEM can face, and uncover Adobe security best practices.
Placing emphasis on AEM security best practices
Adobe Experience Manager has established partnerships with software development companies, leading researchers, and security research institutions to keep up with the latest vulnerabilities and cyber threats. To put a few on your radar, Adobe collaborates with:
- Information Systems Security Association (ISSA)
- Open Web Application Security Project (OWASP)
- Center for Internet Security (CIS)
- and an array of other providers
A powerful content management system such as Adobe Experience Manager strives to incorporate optimal security techniques, ensuring quality and safety. Adobe has been continually perfecting AEM with every version released. But the fundamental established structure is what holds the CMS together. Adobe AEM vulnerabilities aren’t easily found.
Basic AEM infrastructure
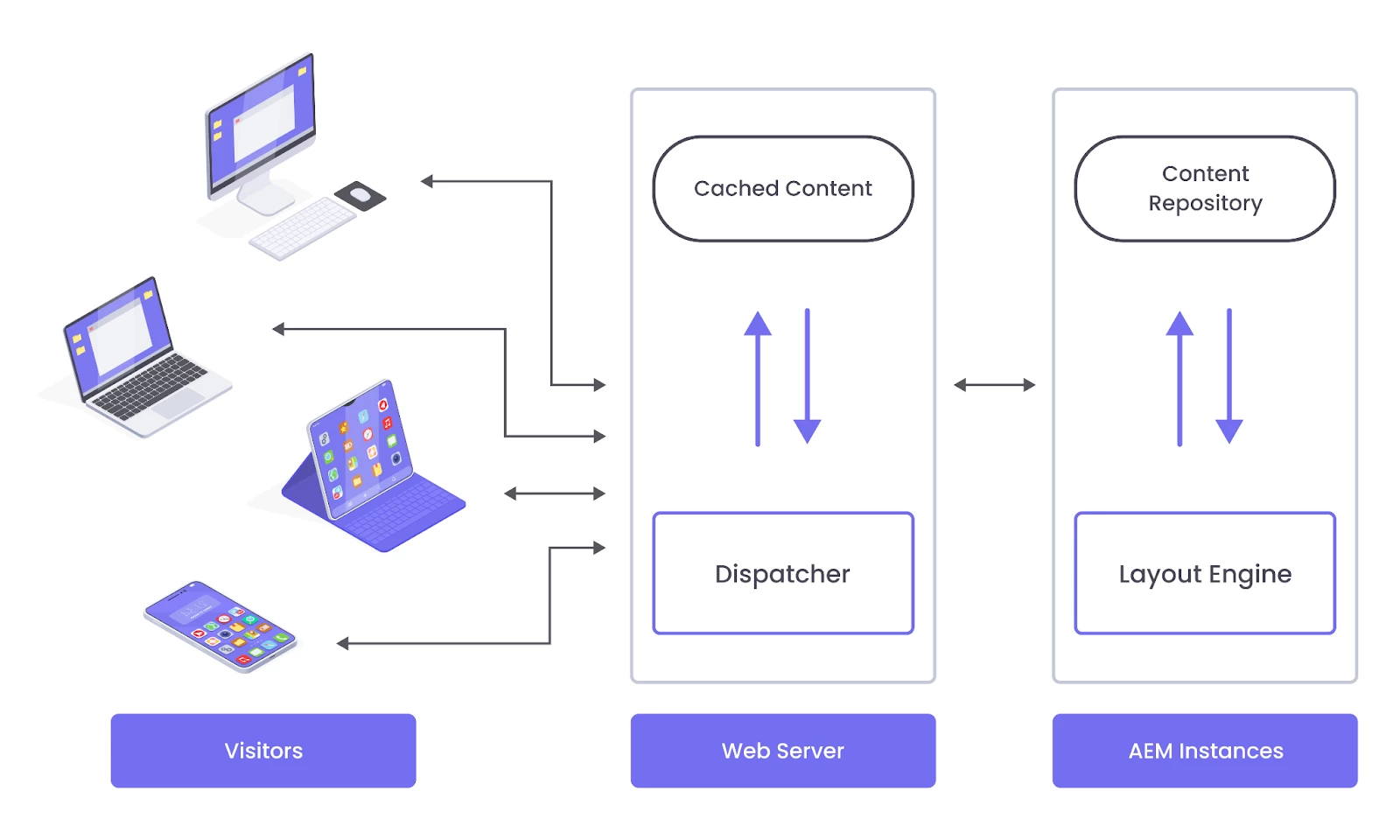
AEM infrastructure falls into three basic levels: web application server, web application framework, and content repository.
On the web application server, you can deploy AEM in a standalone mode. In other words, it’s the level where your website is live. The web application framework allows you to create RESTful, content-oriented sites based on the Sling Web Application Framework.
The AEM content repository is like a well-structured database that stores content, code, templates, and any other data used by the application.
All three levels are interconnected and let you create your web application with Adobe AEM security in mind. How you deploy your website in order to avoid vulnerabilities is where it gets tricky.
Typical AEM deployment scenario
AEM consists of instances that fall into two types: Author and Publish. Author instances in AEM are a place for creating, uploading, and editing content, as well as administering the website. While Author instances give you a behind-the-scenes peek, Publish AEM instances are where your content becomes public. All AEM instances utilize the same software, but Author and Publish instances are configured differently.
AEM Dispatcher is another vital layer in Adobe Experience Manager infrastructure. AEM Dispatcher is a web server that caches web pages produced by Publish instances and balances the load a web application receives. (Web servers shouldn’t be confused with the server where your files and other data are stored.) Instead of sending all the queries to the content repository all the time, AEM Dispatcher fetches and stores content to serve it on demand. This is especially useful for better web application performance, reduction of server response time, and helping web pages load faster.
Source:
Besides being a load balancer and a caching mechanism, AEM Dispatcher filters incoming requests from website visitors and protects your environment from malicious queries. You need to configure AEM Dispatcher because default configurations may not be enough to deliver the necessary level of security. Follow the AEM Dispatcher Security Checklist to make sure you include every single detail into your configurations.
Cybercriminals are aware of the AEM structure and try to come up with attacks that can jeopardize Adobe Experience Manager or any other CMS.
Cyberattacks that can exploit Adobe AEM vulnerabilities
Typically, cyberattacks aim to find AEM security vulnerabilities and exploit them to get access to restricted files or sensitive data. We’ve put together this rundown of major threats that can create bottlenecks for seamless performance of your solution.
SQL injection attacks
SQL injection is an attack that interferes with a harmless query an application makes to the database. With a SQL injection, an attacker can access data that belongs to other users or any other data. The attacker can then modify or delete data, which will lead to changes in the application’s content or behavior.
DoS attacks
Denial of Service or DoS attacks are widespread among CMS software and aim to make a website fail to receive real visitors. During the attack, fake requests are sent to the website to overload the server where the website resides.
Cross-scripting attacks
Cross-scripting or XSS attacks are directed at trustworthy and reputable sites. An XSS attacker tries to inject malicious code in the form of a browser-side script that end users may receive. This malicious code can affect the way the page is displayed in a browser, access cookies, or other sensitive information used on the website.
Directory traversal attacks
Directory traversal or path traversal attacks aim to access restricted directories and files to change an application’s data or behavior, and, if possible, take full control of the server.
Brute force attacks
With brute force attacks, a cybercriminal runs a program that tries to come up with an exact combination of user names and passwords to access an account.
Listing all attacks would probably require an article of its own. Yet bespoke attacks are common for detecting Adobe AEM vulnerabilities. Wondrously, there’s a remedy, and it lies in how much you’re willing to use the tools created for better Adobe Experience Manager security.
How to mitigate AEM security vulnerabilities
Prevention is the best medicine. AEM does everything possible to build a safe environment, and so should you on your end. Implementing basic measures of precaution can help you run an AEM environment effectively.
Utilize penetration testing before production
To make your AEM environment secure, you need to test it before moving it to production. Penetration testing is one of the key AEM security best practices Adobe recommends you do. With penetration testing, you simulate cyber attacks to detect weaknesses or ways to exploit the system. Additionally, you can study the list of AEM security vulnerabilities and see which ones apply to your version of AEM.
Follow the Adobe AEM security checklist
Always run a security check according to the AEM security checklist. The list gives you guidelines and examples of how you can check your Adobe AEM security on the CMS level. The checklist also walks you through other configurations with the aim of protecting your system from malicious behavior.
Host your project with care
Besides finding a team that can develop a safe AEM ecosystem, hosting is an integral part of mitigating AEM security vulnerabilities. It can significantly contribute to Adobe security best practices. You can opt for hosting your AEM infrastructure on-premise, in Adobe Experience Cloud, or using managed hosting such as Adobe Managed Services.
If you choose to run your website on-premise, your IT team will be monitoring the server, troubleshooting issues, and configuring the environment to meet your specific project needs.
Adobe Experience Cloud allows you to deploy, host, scale, and protect your CMS in the meantime. Adobe becomes responsible for mitigating AEM security vulnerabilities.
With managed hosting offered by Adobe Managed Services, you free your IT specialists and delegate any Adobe AEM security hassles to a dedicated team.
Secure your AEM through HTTPS
Your AEM environment should only use an HTTPS connection. The browser notifies users about an unsecured connection, which results in high bounce rates. Secure both authoring and publishing instances with HTTPS that encrypts data traveling from the web server to the user and vice versa.
Enable encryption through CryptoSupport
Adobe Experience Manager lets you connect to third-party services at will. However, it may unintentionally make your solution vulnerable to cyberattacks unless you keep to AEM security best practices.
When connected to third-party services and acting by itself, your CMS stores credentials and sensitive data which are to be encrypted. Encryption allows you to cipher credentials and data, which you can then decipher with a special key.
AEM has an in-built CryptoSupport service that provides encryption for every AEM instance through a unique key. This key helps cipher and decipher sensitive data, credentials, and so on. In case you need to replicate the encyrption key and apply it to all AEM instances, you can do so with the aim of saving development time while still preserving quality.
Create a unique, strong password for admin accounts
This may be an obvious point, but few people actually pay much attention to creating a strong password. Data breaches happen because passwords are primitive. To prevent unauthorized access to your data in an AEM environment, change the default passwords in the AEM Admin and OSGi Console Admin accounts.
Your passwords should be unique and strong. You should come up with a longer password that contains both lowercase and uppercase letters, along with special characters. To ensure your password is strong, consider running it through a password checking tool.
Additionally, make sure no authoring tools, system consoles, or raw repository data are accessible to the public. Otherwise, your solution might be exposed to AEM vulnerabilities.
Run regular scanning procedures
You can opt for detecting AEM security vulnerabilities on your own by scanning your content management system with a paid audit or open-source tool. When you run your web application through a scanning tool, the program analyzes every URL of your AEM environment. Depending on your scanning program, you should receive a comprehensive list with the results and alerts. The report you get can help you identify, assess, and mitigate risk in relation to AEM security vulnerabilities.
Make use of Adobe AEM security hotfixes
Adobe is especially thorough in releasing AEM hotfixes that you can download and implement. You should install the AEM Releases and Updates when they become available. Be sure to test the hotfixes you install before you actually move them into production.
Set up out-of-the-box tools for monitoring AEM
To overcome the daunting challenge of protecting your system, integrate your AEM environment with the Operations Dashboard. With the dashboard, you can monitor AEM instances for any upcoming bottlenecks and quickly fix components that were reported as having issues.
The Log Message Analyzer is another out-of-the-box tool to support overall Adobe AEM security. It can give you details on where errors occur and how to fix them. The Analyzer can be configured to capture various messages, besides errors, with informational and warning contents you can further analyze.
Make regular backups
No matter whether you host your site on-premise or use Adobe Managed Services, you should have scheduled backups. Backups are on-demand and/or automatic copies of your site that are stored (ideally) on a separate server to avoid data loss. A copy of your site can help you restore a file or an entire AEM environment back to normal, as it was before a disruption occurred.
Safeguard your site by following AEM security best practices
Adobe Experience Manager has a complex infrastructure that should be protected — and it is! The key to Adobe AEM security is the ability to configure the system, run penetration testing before publishing, perform regular scanning, and stay tuned for AEM hotfixes. The human element can also be a cause of AEM vulnerabilities, so you should conduct information security training for any team members you welcome onboard.
So let us build websites with AEM security best practices in mind and give valuable experiences to your customers, armed with AEM best practices!
Here are the authors of the AEM security article: Petr Juravlev, Denis Glushkov, Angela Beklemysheva
Thank you so much for contributing!