How do you render html in jcr type:String field through custom component htl?
I've got several type:String fields in my jcr properties that I need to render through the htl script of a custom component. Don't know if this matters, but these String fields are populated from multi-line fields of a content fragment.
In my component code, I have the ContentFragment, and for jcr fields that were populated by single-line text fields on the content fragment model (and thus have no html tags in them), they render fine if I do something like this:
@Override
public String getTitle() {
ContentElement titleElement = pageContentFragment.getElement("insight-title");
return titleElement.getContent();
}
and then in my htl, something like this:
<section
data-sly-use.insight="com.ab.bernstein.core.models.InsightHero"
data-sly-use.placeholderTemplate="core/wcm/components/commons/v1/templates.html"
>
<div>
<h1>${insight.title}</h1>
</div>
</section>
But for those fields that have html tags like this:
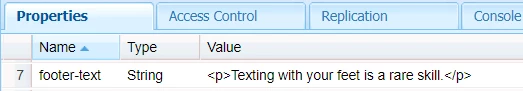
The same approach displays the p tags on the page instead of inserting them into the html dom. The actual dom generated looks like this:
<p><p>Texting with your feet is a rare skill.</p></p>
Is there a way from within my component code to prevent AEM from escaping the HTML like this?

