SAML | IDP Certificate through CURL
Hi All,
Am looking into options on how to configure SAML on our AEM instances, especially uploading truststore and keystore.
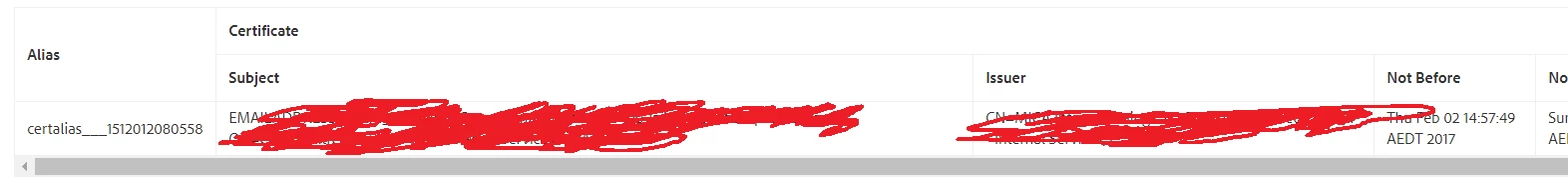
From the documentation, we understand that we can go to admin console and manually upload the certificates, but they are manual steps and biggest issue is the truststore alias is random number which is restricting us to put SAML config in source control.
Can you let us know if there is any other option to upload the truststore and keystore into AEM instances, say through CURL?
Also, is there a way to predefine the truststore alias key?
Note: Tried below solution but not working in 6.2