Digital Ad Fraud

Digital marketing is a growing, multi-billion-dollar market. The sheer size of this market tempts hackers & criminals to create techniques/technologies to steal money from the advertisers.
Ad fraud phenomenon exists since beginning of digital advertising, but in recent years it has been gaining traction as the RTB (real time bidding) model is now being widely adopted. That’s because, the fragmented nature of RTB makes easier to commit & conceal fraud.
Have you ever wondered, how much of the internet is fake? There was an article in New York Magazine recently, “fake people with fake cookies and fake social media accounts, fake-moving their fake cursors, fake-clicking on fake websites”, this article went on to note that around half of the web traffic has been non-human.
It is estimated that $6 billion is being stolen from advertisers every year due to digital ad fraud, but some type of ad frauds are not easy to detect & the technology to protect advertisers is immature, so the actual figure may be much higher than $6 billion.
Let’s understand some major ad fraud techniques in detail –
1. Hidden/Invisible Ads
The idea behind this fraud is to hide ads on the website & report impressions since the ad appears invisibly. With the number of reported impressions, publishers generate revenue claiming ad delivery. This happens using one of the following techniques:
- Display ad in a 1X1 pixel iframe.
- Display the ads outside viewport area (the visible portion of the entire webpage).
- Display multiple re-sized ads.
- Display multiple ads in an iframe loaded to a single ad slot, which means that out of all the ads loaded, only one will be visible to user.
2. Fake Impression Delivery
The advertiser carefully selects publisher inventory basis on relevant audience and content that coincides with brand by usually paying high CPM rates.
With fake impression delivery ad fraud, part of the ad impressions brought by the advertiser are served on fraudulent websites where neither audience nor the content is relevant to brand. These websites are generally high traffic sites with illegal content which are traditionally hard to monetize.
Now the question arises, with advance reporting & transparency these days how publishers can fake advertisers with fake impression delivery? Through number of redirects and nested ad calls through iframes, the ad calls are ‘laundered’ so the advertisers see legitimate sites instead of actual, fraudulent sites where ads are displayed.
3. Ad Hijacking
Malware hijacks the ad slot on a website and displays ad, generating revenue for the attacker rather than for publisher (website owner). This can be done though one of the ways explained below –
- By changing DNS resolver of user’s computer i.e. resolving ad.doubleclick.com to the IP of the server controlled by the attacker and serving different ads through attacker’s IP.
- By changing ad tags placed by the publisher to ad tags controlled by the attacker.
- Compromising user’s proxy server or router to spoof DNS server or change the HTML content of the site.
4. Click Hijacking
When a user clicks on an ad, attacker redirects the user to a different site by stealing client from advertiser. This is also done using similar techniques –
- By changing DNS resolver of user’s computer.
- Hijacking the click by compromising publisher’s website. Attacker can insert an onClick event on the iframe with the ad.
- Compromising user’s proxy server or router to spoof DNS server or change the HTML request of the site.
5. Pop-under Ads
These are pop-up windows with ads. These ads appear behind the main web browser window, rather than in front. This is considered as a legal advertising method, but most of the ad networks forbid ads served in this way.
If pop-under advertising is combined with fake impression delivery technique, attackers can generate additional revenue.
6. Bots Traffic
Some publishers use botnet traffic, which consists of compromised user’s computers/set of cloud servers & proxies, to achieve higher revenue targets, ensure eCPM growth & to maintain audience growth.
Methbot is considered one of the biggest & most profitable digital ad fraud detected in 2016. Methbot, discovered by WhiteOps is controlled by Russian criminal group was estimated to pull in $3m to $5m from advertising everyday.
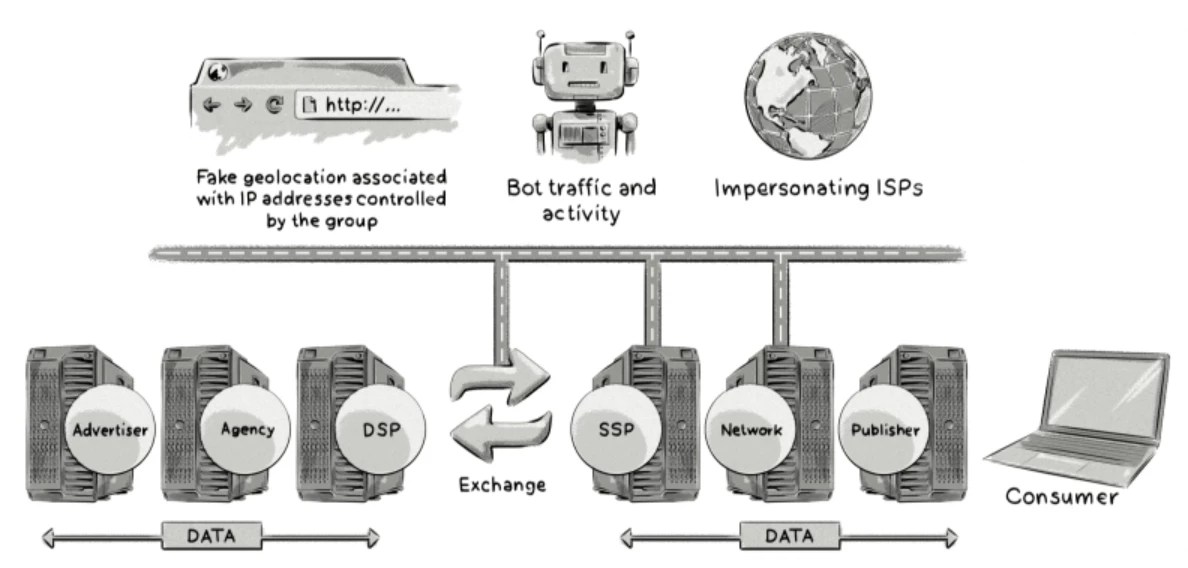
Methobot was carefully planned and it compromised the ad delivery chain. It not only impersonated premium sites, but also fabricated their inventory & disguised itself as legitimate ISPs. Using this, methbot generated fake/human like traffic which opened ads on these fake premium sites, with fake registrations. Methbot gamed the system by deciding, where the most profitable ads should serve & ensuring their fraud web space was purchased at max. profit.
Methbot disrupted exchanges, SSPs & ad networks in the ad delivery chain.
7. Fake Users
Fraudsters also use mobile apps to imitate human like activity. It involves bots, malware & click/app install farms to build large audiences of fake users.
Click bots are created to perform fake in-app actions. The advertisers are tricked to believe that large number of real users clicked their ads while the ads never reach organic audience.
Click farms use people who physically click through the ads, earning CTR money for the fraudsters.
8. Fake Installs
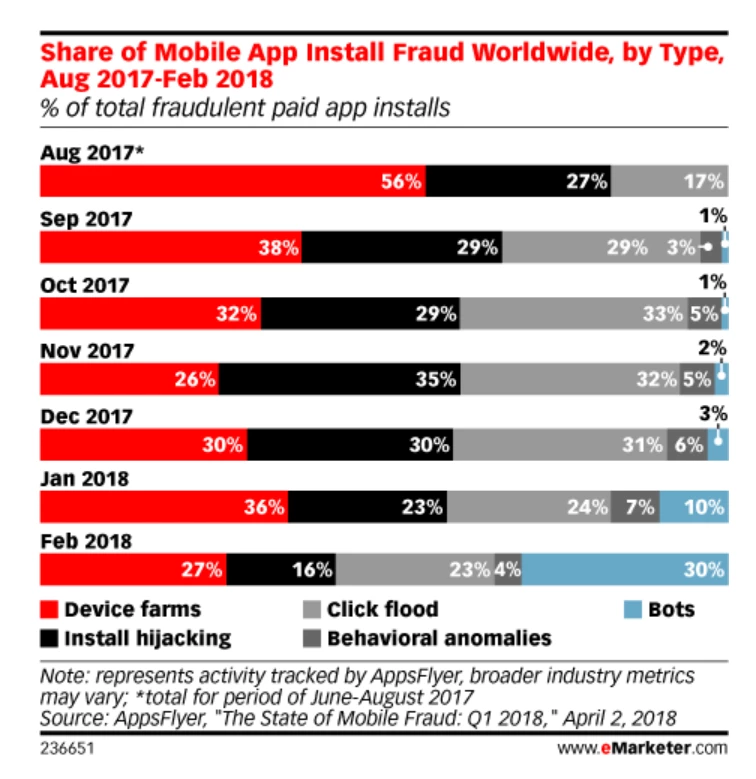
Install farms are another way to imitate human like behavior. They install apps using real people as dedicated emulators (hardware/software that enables one computer system to behave same as another computer system).
Fraudsters also use emulators to mimic real mobile devices. To remain untraceable, device farms regularly reset their DeviceID & avoid detection using new IP addresses.
Fraudsters are targeting mobile apps these days. This is mainly because ads in mobile apps are rarely blocked by ad-blocking software. Also, android is generally considered more vulnerable due to its open ended architecture.
Bots are the pieces of malicious code that perform an action. Bots aim to send clicks, installs & in-app events for installs that never actually happened.
Objective of click fraud is to fabricate clicks on CPC based advertisements by 2 ways –
- Click injection: Fraud apps downloaded by users generate fake clicks & take credits for installation of other apps.
- Click flooding: Hijacked mobile IDs are used to send fake clicks. When a real user with that ID organically installs an app, the fake click will get the credit & make profit.
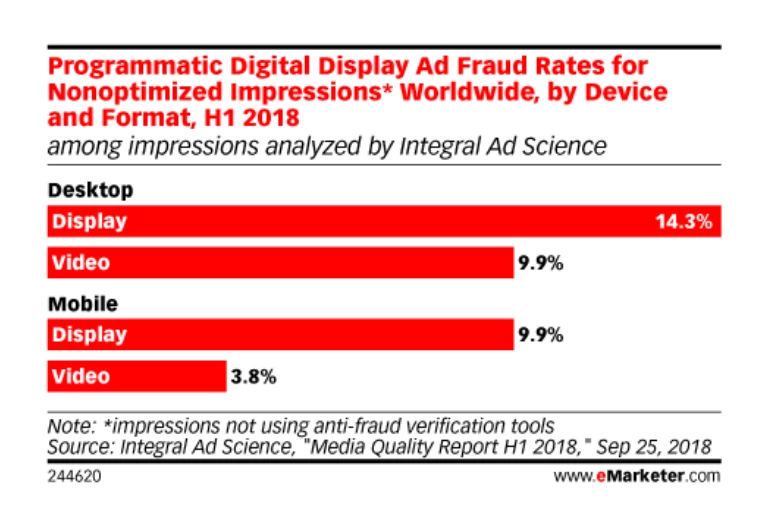
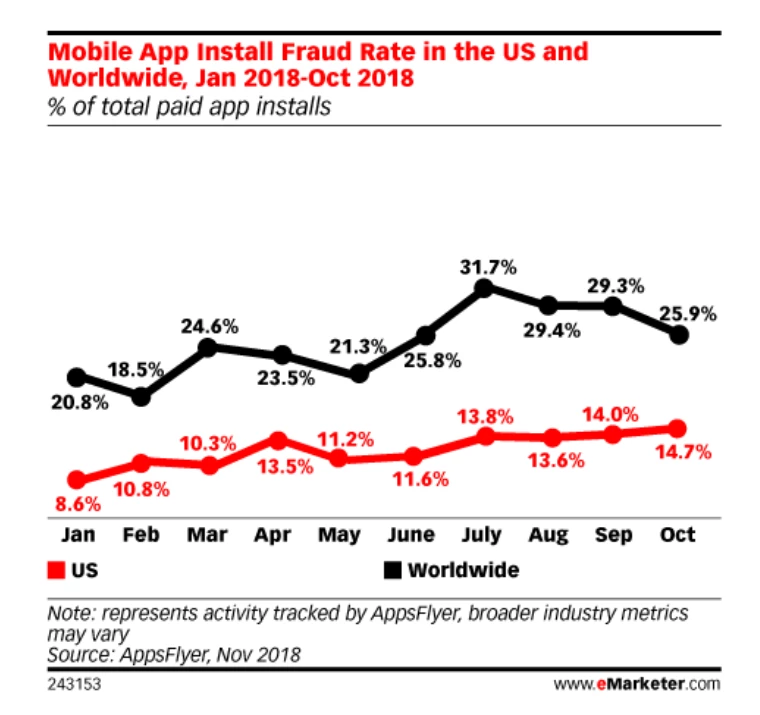
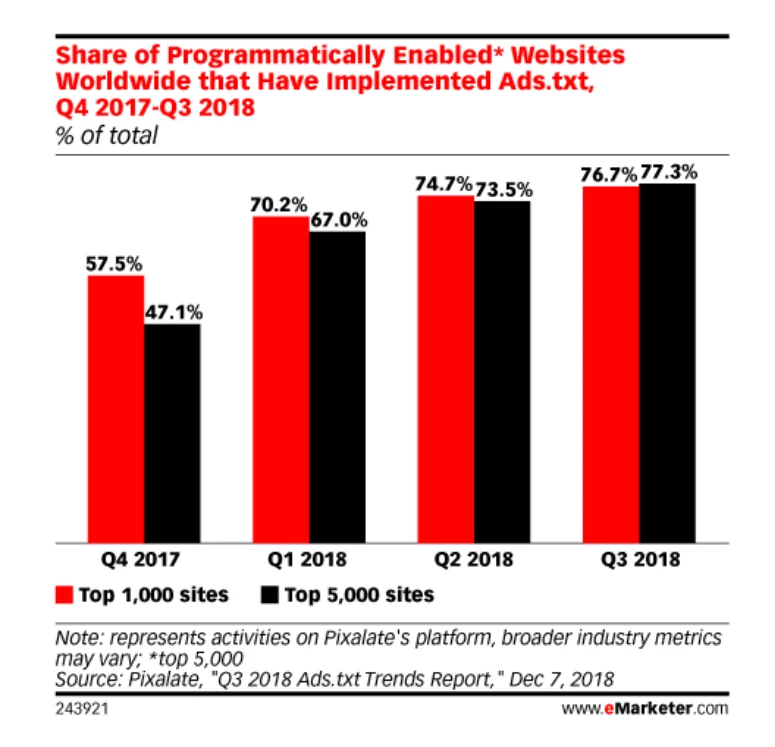
Sharing below, some of the interesting surveys from eMarketer on recent ad frauds happened worldwide -
Solution?
There are number of tools available to help fight against digital ad fraud. These include –
Ad Verification Service
This allows advertisers to check if their ads are displayed in the right context, on the right websites, in the right area of website & seen by the right audiences. Ad verification services are used by advertisers to verify the designated attributes of served ads match their specified requirements in the campaign settings. To do this, verification tags are implemented along with the ad to analyze the content of the publisher’s page & ensure the site is appropriate for the ad.
Ad Verification vendor sends report back to the advertiser/agency, so they can analyze data. Generally, advertiser/agency will have a separate login to ad verification vendor, however some are more seamlessly integrated, with DSP.
Ad verification does not prevent suspicious ads showing altogether, especially when ad is displayed, RTB auction already happened. But, it can help fend off the publishers with low viewability/high fraud traffic by excluding/blacklisting them in the DSP.
Ads.txt
Ads.txt (authorized digital sellers) is an IAB initiative. It specifies the text file that publishers can host on their web servers, listing the authorized sellers of their inventory.
By Nov 2017, more than 44% publishers had ads.txt files. More than 90,000 sites were using ads.txt.
However, ads.txt doesn’t fix all types of ad fraud. It only aims to weed out domain spoofing & arbitrage. The rollout of ads.txt is not just about publishers. DSPs and other ad tech partners have had to change how they work so they can allow buyers to bid only on compliant inventory.
Conclusion
Ad Fraud is a serious problem infusing the advertising industry & the losses it causes are hit the roof. But it does not mean that advertisers should stop advertising. There are various technologies allowing them to detect, prevent & measure specific types of fraud. However, despite advances in technology, digital ad fraud still appears to be a problem that will linger for many years to come due to continuous growth of digital ad spend.
