Saving password inTranslation Cloud config
- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
For the configuration of our translation connector we need to save a password in its Translation Cloud configuration. This used to be ok in AEM 6.5 as the password could be encrypted using the /system/console/crypto. This is no longer possible in cloud based AEM.
Is there a way to programatically invoke the same functionality, when the config form is saved?
Solved! Go to Solution.
Views
Replies
Total Likes
- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hello Arun!
Thanks for the reference, however I don't see how that answers the question.
Let me try to clarify what the problem is.
Formerly, these used to be the steps the user of our connector would take to set up the configuration:
- Create the configuration
- Open /system/console/crypto
- Encode the password to our service
- Fill the encoded password and other details
- Save the configuration
Step 2 and 3 are no longer possible in cloud. I was asking if there is a way the code of our connector could invoke the crypto service to encode the password when the configuration is saved, so that it isn't stored in plaintext.
Or is it the case, that we need to instruct our users to extract the key from their cloud AEM, inject it into an SDK and encode the password there?

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Please check https://experienceleague.adobe.com/docs/experience-manager-cloud-service/implementing/developing/aem...
In case you depend on CryptoSupport (either by configuring the credentials of Cloudservices or the SMTP Mail service in AEM or by using C...), the encrypted properties will be encrypted by a key that is autogenerated on the first start of an AEM environment. While the cloudsetup takes care of automatically reusing the environment-specific CryptoKey, it is necessary to inject the cryptokey into the local development environment.
Arun Patidar

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hello Arun!
Thanks for the reference, however I don't see how that answers the question.
Let me try to clarify what the problem is.
Formerly, these used to be the steps the user of our connector would take to set up the configuration:
- Create the configuration
- Open /system/console/crypto
- Encode the password to our service
- Fill the encoded password and other details
- Save the configuration
Step 2 and 3 are no longer possible in cloud. I was asking if there is a way the code of our connector could invoke the crypto service to encode the password when the configuration is saved, so that it isn't stored in plaintext.
Or is it the case, that we need to instruct our users to extract the key from their cloud AEM, inject it into an SDK and encode the password there?

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Arun Patidar

Views
Replies
Total Likes
- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Views
Replies
Total Likes

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Arun Patidar

Views
Replies
Total Likes
- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hello @arunpatidar ,
Thanks for the tip, the event route turned out to yeild a working implementation.
I still have one concern though.
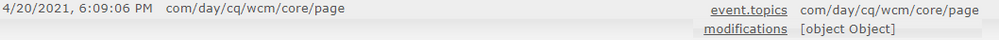
The event that is published when the configuration is saved has the broad topic of `com/day/cq/wcm/core/page`, so filtering on level of code seems like a potential performace issue.
But I'm unable to filter events using the `EventConstants.EVENT_FILTER`.
I tried to specify
EventConstants.EVENT_FILTER + "(path=/conf*)"
or
EventConstants.EVENT_FILTER + "(modifications.path=/conf*)"
but neither filters out a regular page edit. I suspect this is caused by the event having the modifications as an object (see attached screenshot from the event console).
Do you know if there is a way around that, or if filtereing in the event handler itself is actually the correct solution?

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hi, can you check below example that works for me for sling events
https://github.com/arunpatidar02/aem63app-repo/blob/master/java/ReplicationEvent2.java
Arun Patidar

Views
Replies
Total Likes
- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Views
Replies
Total Likes

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hi, can you try with below code
package com.community.aemlab.core.events;
import org.osgi.framework.Constants;
import org.osgi.service.component.annotations.Component;
import org.osgi.service.event.Event;
import org.osgi.service.event.EventConstants;
import org.osgi.service.event.EventHandler;
import org.slf4j.Logger;
import org.slf4j.LoggerFactory;
@Component(service = EventHandler.class, immediate = true, property = {
Constants.SERVICE_DESCRIPTION + "=Demo to listen event on page modification ",
EventConstants.EVENT_TOPIC + "=org/apache/sling/api/resource/Resource/ADDED",
EventConstants.EVENT_TOPIC + "=org/apache/sling/api/resource/Resource/CHANGED",
EventConstants.EVENT_FILTER + "=(path=/content/aemlab/us/*/jcr:content)" })
public class PageEvent implements EventHandler {
private static final Logger LOG = LoggerFactory.getLogger(PageEvent.class);
@Override
public void handleEvent(Event event) {
LOG.info("Event is called with paths PageEvent Test ......");
}
}
Arun Patidar

Views
Replies
Total Likes