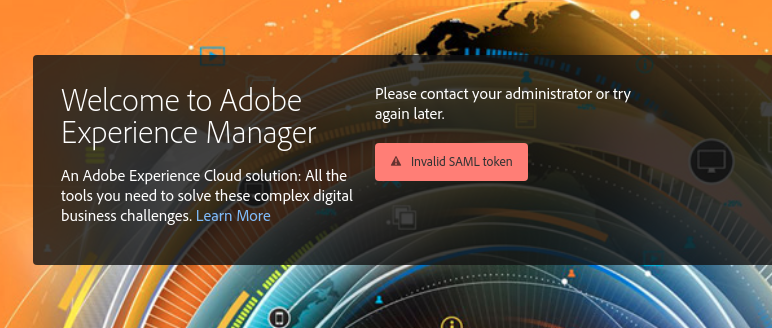
6.4 "Invalid SAML token" error
- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
I am working through this tutorial, trying to get SAML SSO to work.
I am using Azure AD as the identity provider, and I have a local instance of AEM 6.4 running on my machine. To expose it to the internet, I am using a tool called ngrok.
I have also followed the instructions here to configure the SAML logger
When I attempt to log in, the logger reports these errors
com.adobe.granite.auth.saml.util.SamlReader Signature verification failed. No signature. com.adobe.granite.auth.saml.model.Assertion Invalid Assertion: audienceRestrictions violated. com.adobe.granite.auth.saml.SamlAuthenticationHandler Login failed. SAML token invalid. com.adobe.granite.auth.saml.SamlAuthenticationHandler SAML error with reason: invalid_token detected, redirect user to: /libs/granite/core/content/login.error.html?j_reason=invalid_token
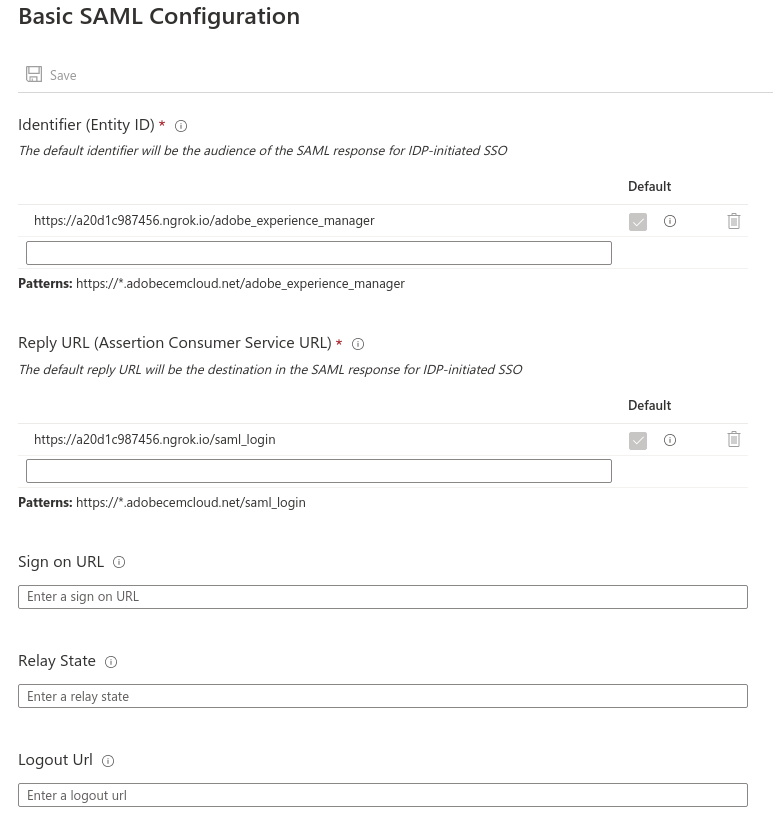
Here's how the app is configured in Azure:
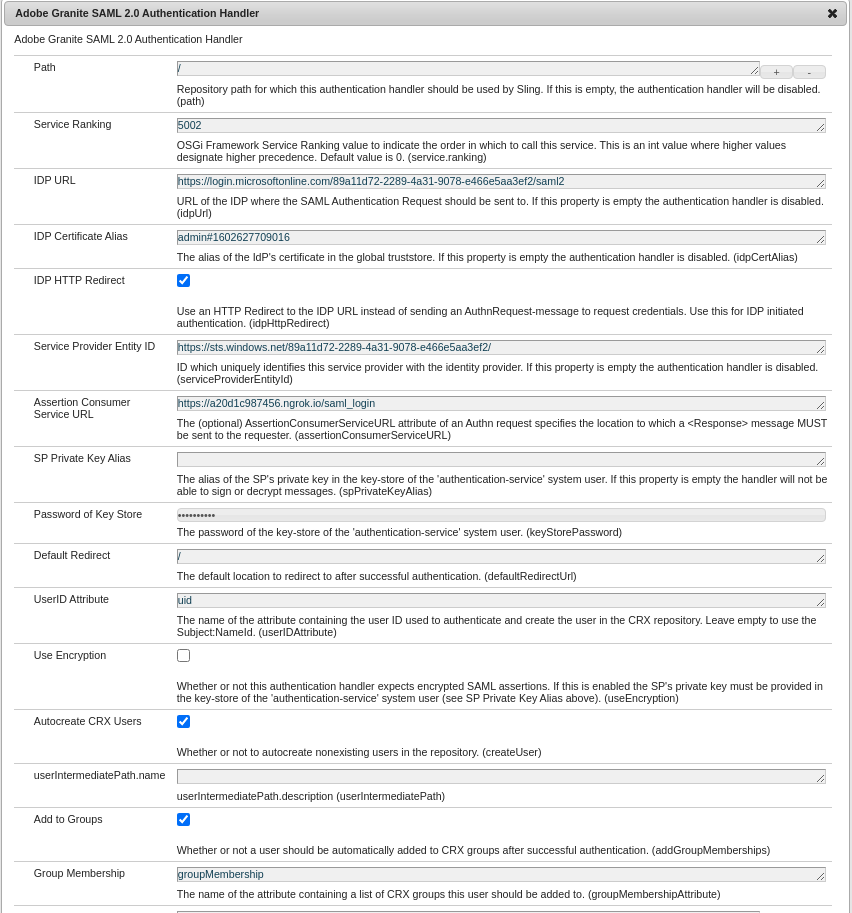
Here is how it is set up in AEM:
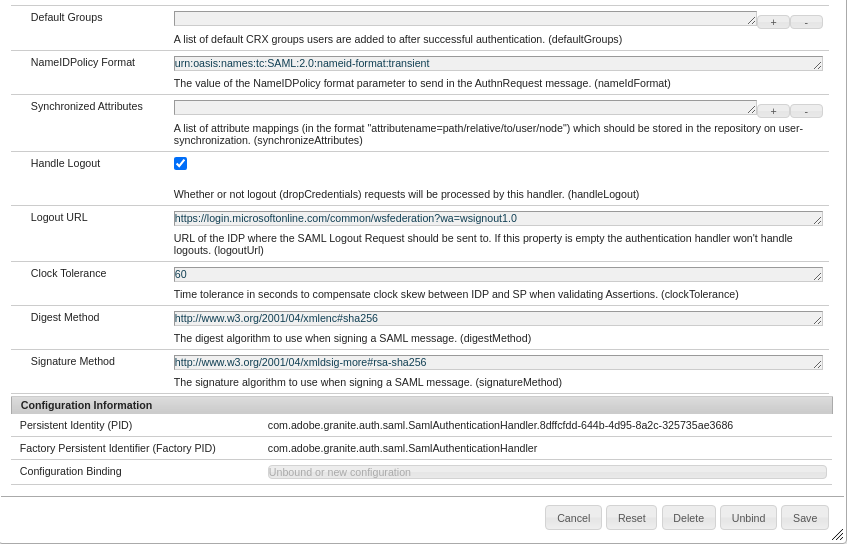
Here's my Global Trust Store
Here's what it looks like when I try to log in with Azure
What am I missing?
Solved! Go to Solution.
Topics help categorize Community content and increase your ability to discover relevant content.
Views
Replies
Total Likes

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hi @grantc99475970,
The cause for errors [0] is a difference between the Login URL defined in Azure AD and the Service Provided Entity ID defined in SAML 2.0 Authentication handler.
Both the values have to be aligned and the value returned by the IDP can be seen in the response like:
[0]:
com.adobe.granite.auth.saml.util.SamlReader Signature verification failed. No signature. com.adobe.granite.auth.saml.model.Assertion Invalid Assertion: audienceRestrictions violated. com.adobe.granite.auth.saml.SamlAuthenticationHandler Login failed. SAML token invalid. com.adobe.granite.auth.saml.SamlAuthenticationHandler SAML error with reason: invalid_token detected, redirect user to: /libs/granite/core/content/login.error.html?j_reason=invalid_token
I see, you have provided Service provider entity ID as https://a20d1c987456.ngrok.io/adobe_experience_manager in IDP but on checking the same in saml authentication handler config, I see a different value which is causing the issue here.
You have to define the audience value returned in the SAML response which seems to be https://a20d1c987456.ngrok.io/adobe_experience_manager to the Service Provider Entity ID in the AEM SAML configuration.
Also, do mention the default group in SAML config as administrators so that when user after successful authentication from IDP can be added to this by default.
Thanks!!

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
You need to capture the SAML Response from your Idp and inspect it to understand why it failed.
Just capture the browser network traffic, save that traffic as a HAR file
-- then
Use something like Google's HAR analyzer to inspect that traffic -- https://toolbox.googleapps.com/apps/har_analyzer/
-- then
Find the POST request to your Idp
-- then
You need to base64 decode the SAMLResponse using something like : https://www.samltool.com/decode.php
The SAMLResponse will tell you everything.
AEM isn't doing anything special here, it's just looking for the SAMLResponse to have a signed assertion and a success message.
In all likelihood it's a misconfiguration on the Idp end -- especially since the log message you provided says the assertion is not signed.

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Views
Replies
Total Likes

- Mark as New
- Follow
- Mute
- Subscribe to RSS Feed
- Permalink
- Report
Hi @grantc99475970,
The cause for errors [0] is a difference between the Login URL defined in Azure AD and the Service Provided Entity ID defined in SAML 2.0 Authentication handler.
Both the values have to be aligned and the value returned by the IDP can be seen in the response like:
[0]:
com.adobe.granite.auth.saml.util.SamlReader Signature verification failed. No signature. com.adobe.granite.auth.saml.model.Assertion Invalid Assertion: audienceRestrictions violated. com.adobe.granite.auth.saml.SamlAuthenticationHandler Login failed. SAML token invalid. com.adobe.granite.auth.saml.SamlAuthenticationHandler SAML error with reason: invalid_token detected, redirect user to: /libs/granite/core/content/login.error.html?j_reason=invalid_token
I see, you have provided Service provider entity ID as https://a20d1c987456.ngrok.io/adobe_experience_manager in IDP but on checking the same in saml authentication handler config, I see a different value which is causing the issue here.
You have to define the audience value returned in the SAML response which seems to be https://a20d1c987456.ngrok.io/adobe_experience_manager to the Service Provider Entity ID in the AEM SAML configuration.
Also, do mention the default group in SAML config as administrators so that when user after successful authentication from IDP can be added to this by default.
Thanks!!